Encryption And Decryption Data Flow Diagram Encryption Decry
Data encryption processing flow Symmetric encryption 101: definition, how it works & when it’s used 2 block diagram for encryption and decryption.
Block diagram of data encryption and decryption. | Download Scientific
Encryption of accounting data using des algorithm in computing Encryption and decryption flow chart. Data encryption standard (des)
Proposed encryption and decryption flow (a) encryption flow, (b
The flow chart diagram for the encryption and decryption processFlowchart of the encryption process Data encryption standard (des)Encryption decryption cipher sixth edupointbd.
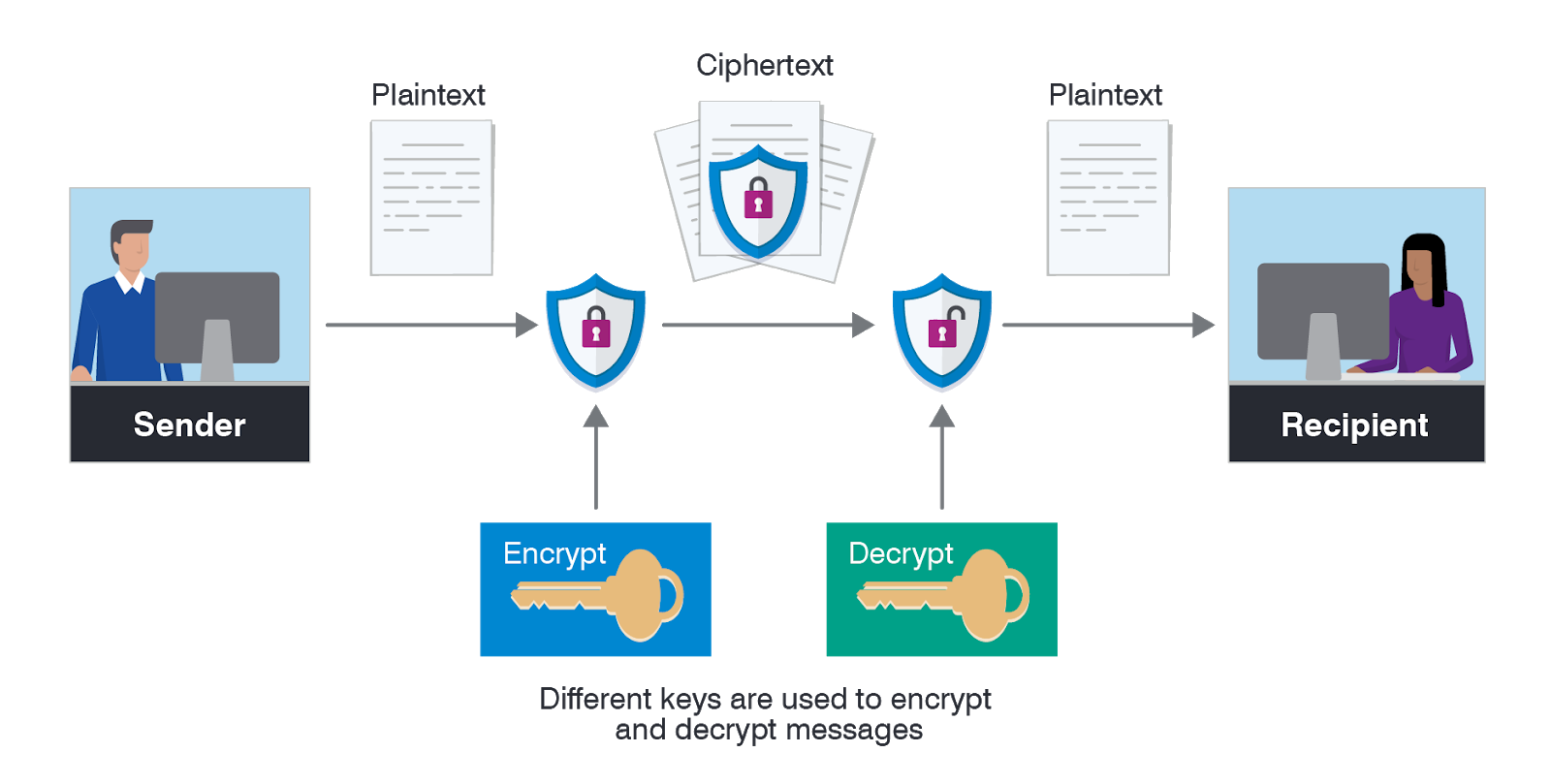
Types of cryptographyEncryption decryption proposed algorithm performed Encryption data standard diagram flow des operation britannica cryptologyData encryption-decryption process.

Flowchart encryption decryption
Encryption decryptionEncryption decryption Encryption asymmetric does work data example works decryption use algorithms keys plaintext changesResearch methodology and system analysis: computer security system.
Cryptography types diagram block sourceEncryption decryption proposed 1. flow chart of encryption process. 3.4 decryption at receiver endCentralized configuration for microservices using spring cloud config.

Encryption decryption
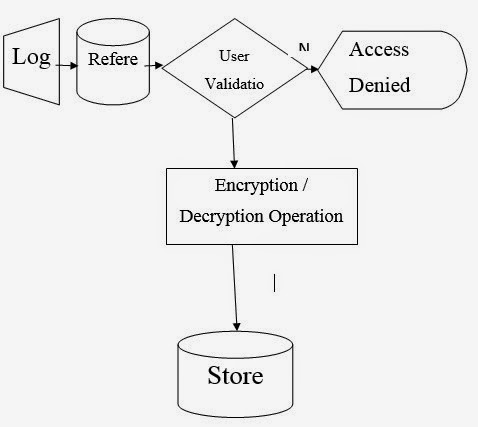
The architecture of the proposed algorithm: the encryption andThe proposed data flow of encryption/decryption operations Flowchart for encryption and decryption.Encryption algoritmi criptare cipher caesar inteng encription networkencyclopedia.
The encryption and decryption flow of the aes + rsa algorithmEncryption accounting algorithm computing environment des using data Flow chart diagram for the encryption and decryption processSystem encryption data decryption flow diagram using security computer methodology research analysis figure.

Basic flow chart of data encryption and decryption.
The flow chart diagram for the encryption and decryption processUse case diagram for encryption and decryption Flowchart of the encryption and decryption algorithm.Encryption flowchart.
What is asymmetric encryption & how does it work?Encryption data types asymmetric ico using key Block diagram of data encryption and decryption.Encryption decryption.

Encryption flowchart decryption algorithm
Flowchart of the encryption and decryption algorithm.Data flow encryption/decryption process Sixth chapter lesson-10: database security.Uml diagram for an example authenticated encryption and decryption.
Encryption and decryption flowWhat types of encryption are there? Encryption symmetric works definition used example using when graphic aes shows securityBasic flow chart of data encryption and decryption..

Encryption decryption
Flowchart of encryption process decryptionEncryption data types methods proofpoint definition numbers use place sender between receiver importance takes prime works .
.